Key takeaways:
- Australian cybercrime now costs large businesses $202,700 per incident on average, making Zero Trust architecture a board-level financial imperative
- Zero Trust is a phased programme, not a product. Identity controls, microsegmentation, and ZTNA must be sequenced deliberately to avoid operational disruption.
- Full ZTA implementation in Australia ranges from AUD 70,000 to 700,000+, but reduces average breach exposure from a potential AUD 4.26 million loss.
- Regulatory alignment with ACSC Essential Eight, SOCI Act, and CPS 234 is structurally built into a well-executed Zero Trust programme, not bolted on afterwards.
Australian Signals Directorate’s Annual Cyber Threat Report 2024-2025 recorded one cybercrime report every six minutes. Even more alarming, the average self-reported cost of cybercrime for large businesses hit approximately $202,700 per incident. High-priority security incidents also rose by 11 percent over the previous year.
Those numbers do not surprise most CIOs we work with. What surprises them is how little their existing security architecture has changed in response.
The legacy perimeter model was designed for a world that no longer exists. Before hybrid work, before SaaS sprawl, before distributed data across multiple clouds. Today’s reality makes zero trust architecture implementation in Australia a strategic necessity, forcing a shift from “trust but verify” to “never trust, always verify,” treating every access request as potentially hostile.
Zero Trust Architecture (ZTA) starts from a fundamentally different premise: no user, device, or connection is trusted by default, regardless of where it originates. Access is verified continuously, privileges are granted at the minimum level required, and lateral movement through systems is structurally prevented rather than detected after the fact.
For Australian enterprises, this shift is no longer optional. Regulatory pressure under the Privacy Act 1988 reforms, SOCI Act obligations, and the Essential Eight maturity requirements from the ACSC all point in the same direction. The question is not whether to move to Zero Trust, but how to do it without disrupting operations or blowing the capital budget.
This article covers the practical drivers behind zero trust adoption in Australia, the architectural pillars that matter most, the migration path that works across industries, and what implementation actually costs in local market terms.
Ready to secure your digital assets against evolving threats?
Speak to Appinventiv’s security engineering team today and get a Zero Trust readiness review tailored to Australian compliance requirements.
Why Traditional Perimeter Security No Longer Works for Australian Enterprises
The castle-and-moat model assumes a fixed perimeter and trusted internal actors. Neither holds in 2025. Understanding how the model broke down is the starting point for any credible Zero Trust business case.
The perimeter security model was coherent when enterprise infrastructure was physically bounded. Data centres were on-premises. Employees worked from offices on corporate hardware. External access was the exception. The logic was simple: build a strong wall, and trust what is inside it.
That logic collapsed under several converging forces. Cloud adoption moved workloads outside the perimeter. SaaS platforms introduced dozens of identity stores IT teams do not fully control. Supply chain integrations opened direct connections to third-party networks. In this context, a VPN is not a security control. It is a remote access tunnel that, once breached, hands an attacker a trusted position inside the network.
The 2020 Accellion breach, which affected Australian organisations including the Reserve Bank of New Zealand and 20+ other state government agencies, exploited exactly this kind of implicit trust. Insider threats compound the problem: in environments without microsegmentation, lateral movement from a compromised workstation to sensitive data can happen in minutes.
Legacy Security vs Zero Trust Architecture
| Architectural Element | Legacy Perimeter Security | Zero Trust Architecture |
|---|---|---|
| Trust Assumption | Implicit trust granted after initial perimeter login. | Zero implicit trust. Verification required for every access request. |
| Access Scope | Broad network access via VPNs and static IP whitelisting. | Microsegmented access restricted strictly to necessary applications. |
| Authentication | Often relies on single authentication without continuous checks. | Continuous, context-aware adaptive authentication based on risk signals. |
| Breach Impact | High risk of unchecked lateral movement across the entire network. | Contained blast radius through strict application isolation protocols. |
| Visibility | Limited telemetry once a user operates inside the firewall. | Granular monitoring of all traffic, user behaviour, and device posture. |
What Are the Key Drivers Behind Zero Trust Adoption in Australia?
Zero Trust adoption in Australia is being shaped by a combination of regulatory mandates, operational realities, and board-level risk appetite changes. Understanding the actual drivers matters because they determine project scope, funding conversations, and the sequence in which controls should be implemented.
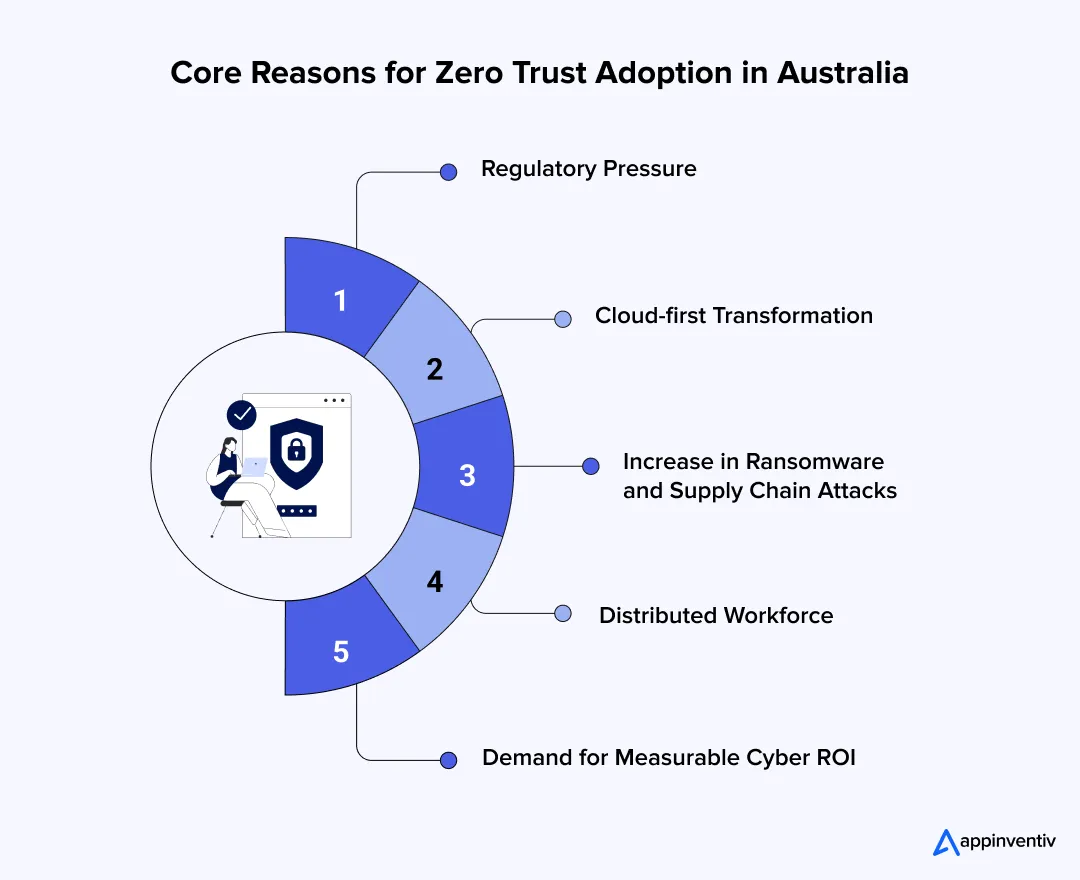
Regulatory pressure is the most immediate force. The Privacy Act 1988 reforms introduce direct liability for senior officers. The SOCI Act extends critical infrastructure obligations to healthcare, data storage, and financial services. For APRA-regulated entities, CPS 234 ties information security capability directly to board governance.
Cloud-first transformation is the second driver. Most large Australian enterprises have moved significant workloads to AWS, Azure, or Google Cloud. Cloud environments have no traditional perimeter. Zero Trust is the natural security architecture for hybrid cloud.
Ransomware has become a board-level conversation. The 2022 Medibank breach exposed data belonging to nearly 10 million Australians. The 2023 Latitude Financial breach affected 14 million records. These incidents have directly funded Zero Trust initiatives that previously sat in the IT backlog.
The distributed workforce is a structural reality across metro hubs, regional offices, mine sites, hospitals, and retail networks. Managing consistent, verifiable security across these environments requires an architecture built for distribution, not retrofitted from one that was not.
7 Core Pillars of a Zero Trust Architecture
A robust security modernisation strategy requires moving beyond fragmented tools to establish a cohesive framework. The foundational pillars of this architecture interlock to ensure comprehensive visibility, strict identity verification, and granular access controls. Executing these elements effectively limits exposure, secures distributed digital assets, and maintains operational velocity without compromising enterprise governance.
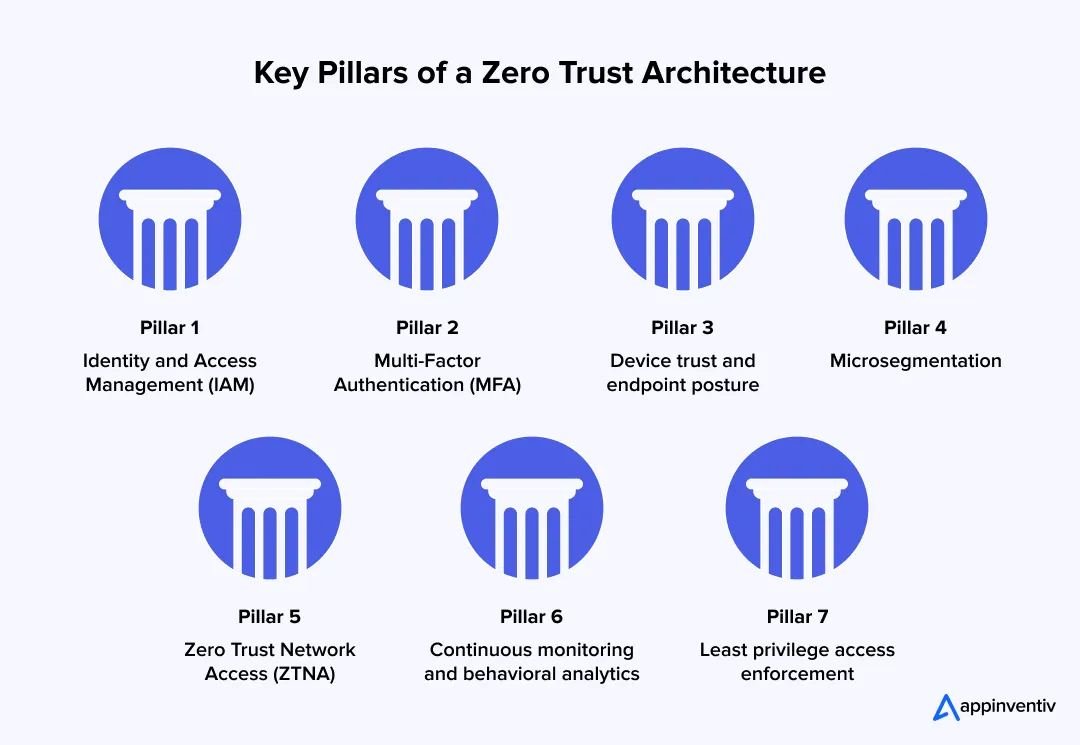
1. Identity and Access Management (IAM)
A mature IAM implementation in Australia is the foundation of Zero Trust. Every access request, whether from a human user, a service account, or a machine identity, must be authenticated and authorised before access is granted. (Think enterprise-grade IdPs like Okta or Ping Identity).
2. Multi-Factor Authentication (MFA)
Multi factor authentication is now a baseline expectation in the Essential Eight framework, required at Maturity Level 1 for internet-facing services. In a Zero Trust context, MFA extends beyond login events to cover step-up authentication for sensitive actions, privileged access requests, and anomalous session behaviour.
3. Device Trust and Endpoint Posture
A verified identity on an unmanaged or compromised device is still a security risk. Device trust controls validate that endpoints meet defined security posture requirements before access is granted. In practice, this means checking patch status, configuration compliance, and whether the device is enrolled in endpoint detection and response (EDR) tooling like CrowdStrike or Microsoft Defender.
4. Micro segmentation
Micro segmentation divides the network into isolated zones at the workload level, preventing lateral movement between applications, services, and data stores even within the same environment. Strict digital boundaries ensure a compromised front-end system cannot be used to breach critical financial databases.
5. Zero Trust Network Access (ZTNA)
Replacing legacy VPNs with ZTNA creates secure, encrypted tunnels directly to specific applications. Internal routing infrastructure remains hidden, drastically reducing the enterprise’s external attack surface.
6. Continuous Monitoring and Behavioural Analytics
Verification extends beyond initial authentication. Continuous telemetry observes active sessions for anomalous behaviour, automatically revoking access if unusual data downloads or erratic access patterns occur.
7. Least Privilege Access Enforcement
Least privilege means granting users and systems only the access rights required for their immediate task, with access expiring or requiring renewal after a defined period. Stripping standing administrative rights is one of the most vital steps to implement zero trust security in Australian enterprises.
Signs Your Enterprise Has Outgrown Legacy Security
Most organisations do not make the decision to move to Zero Trust in response to a single trigger. The decision accumulates from a pattern of operational friction, security incidents, and compliance gaps that individually seem manageable but collectively signal that the architecture has reached its limits.

Multiple disconnected security tools: Operating on fragmented, incompatible security platforms creates severe visibility blind spots, forcing teams to manually correlate logs and delaying threat mitigation.
Increasing ransomware incidents: Frequent near-misses or successful ransomware deployments highlight perimeter failures, allowing malicious payloads to easily bypass firewalls and encrypt flat networks.
Shadow IT and SaaS sprawl: Unchecked proliferation of unauthorised cloud applications obscures corporate data flows, completely undermining enterprise data loss prevention and strict governance strategies.
Insecure third-party/vendor access: Providing external contractors with broad VPN connectivity transforms minor third-party breaches into catastrophic supply chain compromises across your internal network.
Compliance audit fatigue: Struggling to produce accurate, unified access logs during regulatory assessments exposes the organisation to significant financial penalties and governance failures.
Overprivileged accounts: Accumulating legacy user profiles with unnecessary administrative rights provides threat actors with perfect, undetected lateral movement vectors across critical infrastructure.
Difficulty managing remote employees securely: Routing distributed workforce traffic through central corporate hardware causes severe latency, actively encouraging staff to bypass sluggish, mandated security controls.
Slow incident response times: Lacking automated threat telemetry means security operations teams spend hours investigating alerts, allowing breaches to expand before isolation protocols activate.
Industries in Australia Most at Risk
- Healthcare holds highly sensitive data under complex regulatory obligations with limited security budgets relative to data value.
- Banking and financial services face sophisticated threat actors, APRA requirements, and the 2023 Latitude breach as a permanent reference point in board risk conversations.
- Mining and energy operators are managing IT/OT convergence across remote sites where SCADA systems now share network environments with corporate IT.
- Government and defence, retail, and logistics each face the combination of distributed operations, sensitive data holdings, and senior leadership accountability that makes zero trust architecture implementation in Australia a governance necessity, not just an IT decision.
How to Move from Legacy to Zero Trust Security: A 4-Phase Strategy for Seamless ZTA Migration
The migration from legacy security to Zero Trust is an enterprise programme, not a product deployment. You cannot simply “rip and replace” overnight. Successful implementations follow a phased approach that builds capability progressively, limits operational disruption, and creates measurable security improvement at each stage. The following framework reflects what we have found to work across Australian enterprise environments.
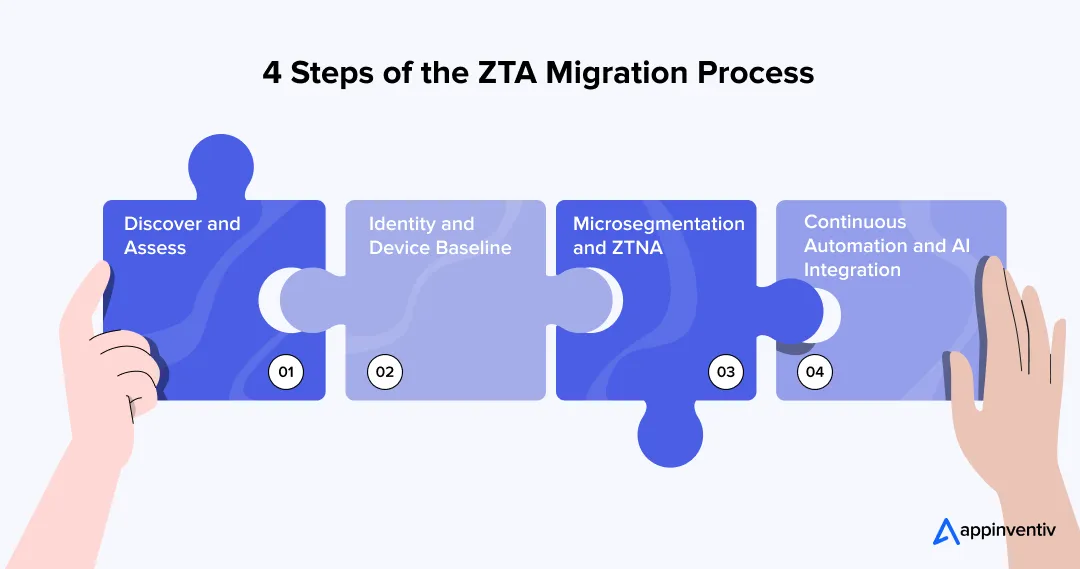
Phase 1: Discover and Assess (Weeks 1-8)
Before any controls are implemented, you need an accurate picture of the environment. This means mapping all identities (human, service, and machine), documenting data flows between applications and systems, cataloguing devices and their security posture, and identifying existing security controls and their coverage gaps.
The discovery phase also surfaces the compliance gap. What does your current posture look like against the Essential Eight maturity targets you are required or intending to meet? Where do SOCI Act obligations create specific control requirements? This analysis feeds directly into the roadmap prioritisation.
Phase 2: Identity and Device Baseline (Months 2-5)
The second phase establishes the identity and device trust foundation. This includes deploying or consolidating IAM, implementing MFA consistently across the environment, establishing device management and posture assessment, and remediating the most egregious over-privileged accounts.
This phase tends to surface significant complexity in legacy environments, particularly around service accounts and machine identities that have accumulated access rights over the years. Managing that remediation without disrupting business operations requires careful sequencing and, in most cases, a parallel-running period during which old and new access models coexist.
Phase 3: Microsegmentation and ZTNA (Months 5-10)
With identity controls in place, the third phase introduces network-level Zero Trust controls. Microsegmentation is implemented progressively, starting with the highest-value data environments and expanding outward. VPN is replaced with ZTNA for remote access, with a carefully managed transition period to avoid productivity disruption.
This phase requires close coordination between the security team, network engineering, and application owners. The segmentation design needs to reflect actual application dependencies, which in complex environments are rarely well-documented and must be mapped through traffic analysis.
Phase 4: Continuous Automation and AI Integration (Months 10+)
The fourth phase shifts Zero Trust from a set of controls into an operating model. Security orchestration platforms integrate signals from across the environment. AI-driven behavioural analytics identify anomalies that rule-based systems miss. Policy enforcement becomes increasingly automated, reducing the manual overhead on security operations teams and improving response times.
In Australian enterprises with mature implementations, this phase also supports the move to continuous compliance monitoring, where audit evidence is generated automatically and compliance posture is visible in near real time rather than reconstructed ahead of scheduled audits.
Also Read: How to Build A Secure App in Australia
Case Study: Zero Trust Architecture Implementation for an Australian Financial Institution
The Challenge: A credit union supporting 1,200 distributed staff faced severe VPN latency that actively hampered customer service. Furthermore, a flat network architecture and overprivileged legacy accounts created critical APRA CPS 234 compliance vulnerabilities.
Appinventiv’s Strategy: We executed a phased architectural upgrade. Our engineering pods rolled out adaptive authentication, replaced failing VPN gateways with Zero Trust Network Access (ZTNA), and applied strict microsegmentation directly around core payment processing workloads.
Measurable Outcomes
- $145,000 in annual licensing savings generated by retiring three redundant legacy security platforms.
- 62% reduction in IT helpdesk tickets related to remote workforce connectivity.
- 100% audit pass rate achieved for external APRA compliance by permanently eliminating unverified lateral network access.
Start your Zero Trust programme with a digital engineering partner who has delivered it before.
Contact Appinventiv Australia for a Zero Trust readiness assessment, compliance gap analysis, and phased implementation roadmap built for Australian enterprise realities.
How Much Does It Cost to Implement Zero Trust Security in Australia?
Budget realism is essential to a credible Zero Trust business case. The cost of zero trust architecture implementation in Australia varies significantly based on organisational scale, existing security maturity, and the complexity of the legacy environment.
On average, for a small to mid-sized Australian enterprise (500-2,000 employees), implementing Zero Trust across all seven pillars typically requires AUD 70,000 to 400,000 over 12-18 months. Larger enterprises with complex legacy environments and OT/IT convergence challenges can expect AUD 400,000 to 700,000+.
The following estimates are based on market rates for enterprise engagements and reflect the full system development cost in Australia, not just licensing.
| ZTA Component | Estimated Cost (AUD) | Key Variables |
|---|---|---|
| Identity & Access Management (IAM) | AUD 10,000 – 100,000 | Number of identities, existing directory infrastructure, cloud vs on-premises mix |
| Network Segmentation | AUD 20,000 – 150,000 | Network complexity, number of applications, OT/IT convergence requirements |
| Security Tools Integration | AUD 10,000 – 100,000 | Existing tool estate, API availability, custom integration requirements |
| Monitoring & Analytics | AUD 5,000 – 100,000 | Log volume, SIEM licensing model, AI analytics platform selection |
| Compliance & Governance | AUD 5,000 – 100,000 | Regulatory scope, maturity assessment depth, audit automation requirements |
| Programme Management & Change | AUD 20,000 – 150,000 | Programme duration, internal change capacity, training requirements |
| Total Programme Investment | AUD 70,000 – 700,000+ | Scale-dependent; excludes ongoing operational costs |
Key Return on Investment Metrics
The ROI calculation for Zero Trust should include both the cost of inaction and the operational improvements.
On the cost of inaction side, the average cost of a data breach in Australia reached AUD 4.26 million in 2024 (IBM Cost of a Data Breach Report). Mature Zero Trust environments report breach probability reductions of nearly 60-70%.
On the operational side, organisations implementing Zero Trust report faster threat detection and containment times, lower overhead from managing disparate security tools, reduced audit preparation costs, and lower cyber insurance premiums in markets where insurers increasingly require evidence of specific controls.
Long-term infrastructure cost optimisation, particularly from consolidating legacy security point solutions into integrated Zero Trust platforms, also contributes to the business case.
What Are Some Essential Regulatory and Compliance Considerations in Australia?
Compliance alignment is not an afterthought in Zero Trust implementation. The most effective programmes are designed with specific regulatory obligations as architectural requirements, not overlays applied after the fact. For Australian enterprises, several frameworks are directly relevant and increasingly complementary to Zero Trust principles.
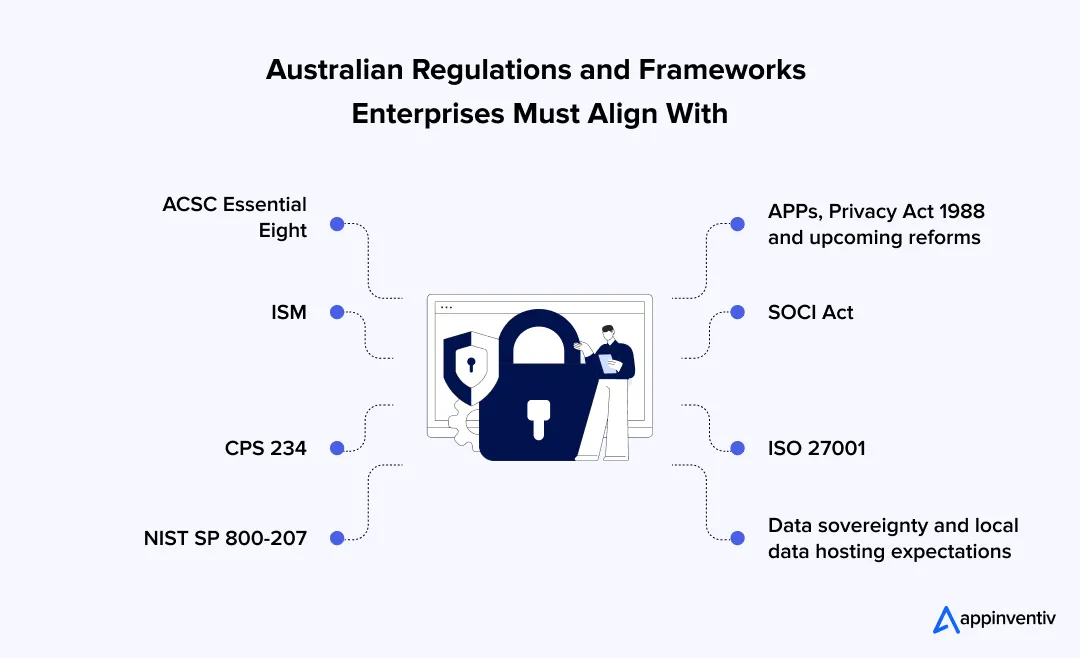
| Australian Framework | Relevant Zero Trust Controls | Priority Sector |
|---|---|---|
| ACSC Essential Eight (ML1-ML3) | MFA, least privilege, patching, application control | All sectors |
| ISM (Information Security Manual) | Access management, monitoring, incident response | Government, Defence |
| Privacy Act 1988 + Reforms | Data access governance, audit trails, breach detection | All sectors |
| SOCI Act | Critical asset protection, access control, risk management | Critical infrastructure |
| CPS 234 | Board accountability, information security capability | Banking, Insurance, Super |
| ISO 27001 | Information security management system controls | Enterprise-wide |
| NIST SP 800-207 | Zero Trust Architecture reference model | Government, Enterprise |
Aligning Zero Trust with Australia’s Essential Eight Priorities and NIST SP 800-207 Guidelines
Essential Eight: Australian enterprises are increasingly expected to align Zero Trust initiatives with the ACSC Essential Eight maturity framework. However, many organisations still struggle to connect identity security, access controls, segmentation, and ransomware resilience into one unified security model.
A well-structured Zero Trust strategy can help enterprises strengthen:
- MFA and privileged access governance
- Legacy VPN and remote access security
- Network segmentation and lateral movement prevention
- Backup resilience against ransomware attacks
- Essential Eight maturity alignment and compliance readiness
NIST SP 800-207: To truly satisfy NIST SP 800-207 guidelines, the gold standard for ZTA, enterprises must logically separate their architecture into three components:
- Policy Engine (PE): The brain that continuously calculates risk and decides whether to grant access.
- Policy Administrator (PA): The executor that receives the PE’s decision and communicates it outward.
- Policy Enforcement Point (PEP): The gateway (like a firewall or endpoint agent) that actively allows or blocks the connection.
What Are Some Core Applications and Advantages of Zero Trust Security Model for Australian Enterprises across Industries?
The operational requirements of Zero Trust vary significantly by industry. The control priorities for a regional hospital managing patient data across telehealth and physical care settings are different from those of a mining company managing IT/OT convergence across remote sites. The following outlines how implementing zero trust architecture in Australia translates into sector-specific outcomes.
Financial Services
Australian banks face CPS 234 and APRA prudential standards, sophisticated threat actors, and complex supply chain dependencies. ZTNA and microsegmentation allow financial services organisations to enable open banking and digital-first channels without granting those services implicit access to core banking infrastructure.
Healthcare
Hospitals and regional clinic systems in Australia share highly sensitive medical records across decentralised networks. Securing telehealth portals requires strict identity verification for both practitioners and patients. By utilising microsegmentation, administrators ensure that compromised administrative software cannot bridge across the network to expose clinical databases or disrupt critical medical devices.
Government
Federal and state departments process vast amounts of citizen intelligence. Delivering digital public services requires robust, identity-native frameworks. Integrating localised access policies ensures that departmental staff only view the specific data sets required for their immediate tasks, maintaining strict sovereign control and preventing bulk intelligence leaks.
Mining and Energy
Resource operators manage heavy machinery across remote Pilbara and Bowen Basin sites. The convergence of Information Technology and Operational Technology creates massive vulnerabilities. Deploying application-level access protocols secures remote diagnostic tools, ensuring that third-party maintenance contractors can optimise heavy equipment without gaining broad access to corporate networks.
Retail and eCommerce
Retail organisations managing customer payment data, loyalty programmes, and supply chain integrations face PCI-DSS obligations alongside the requirements of the Privacy Act. Zero Trust controls support secure payment system isolation, protect customer data across omnichannel environments, and enable secure third-party integrations with logistics and fulfilment partners.
Common Pitfalls in Zero Trust Architecture Implementation in Australia and How Appinventiv Helps Overcome Those Barriers
Executing a security transformation involves operational hazards that frequently stall momentum and inflate budgets. Recognising these structural failure points early prevents enterprises from abandoning their modernization efforts. We align technical execution with commercial realities, ensuring your architectural upgrade navigates legacy complexities and workforce friction without disrupting core business velocity.
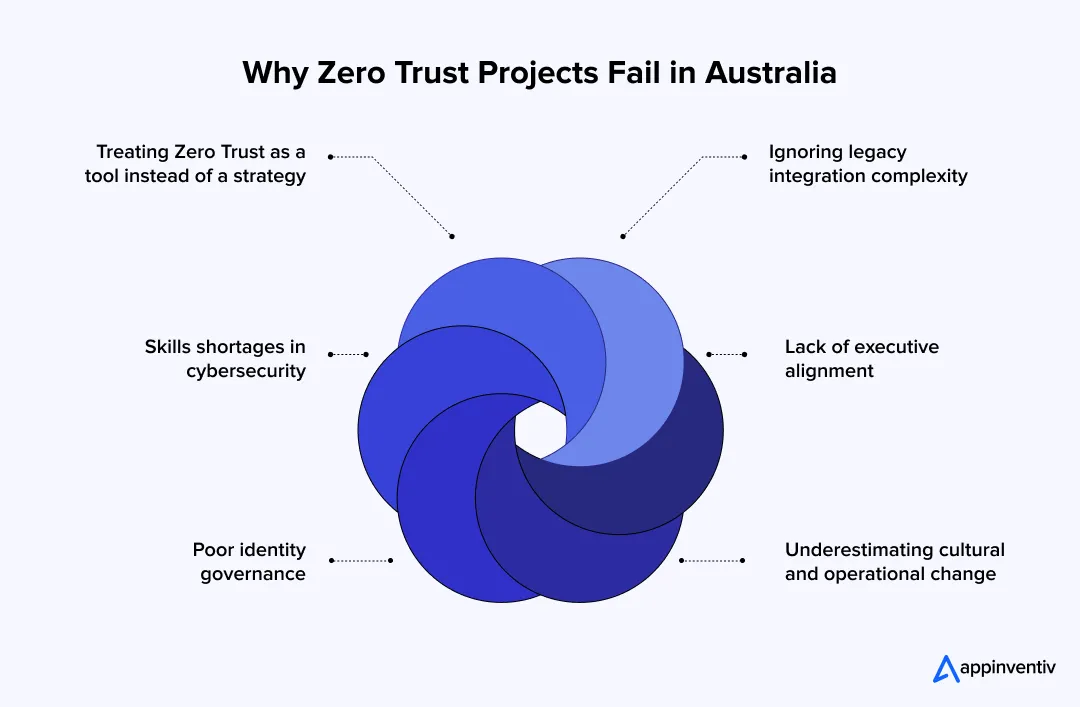
Treating Zero Trust as a Tool Instead of a Strategy
Viewing modernisation as a simple software purchase inevitably leads to fragmented environments. Technology alone cannot fix flawed access policies or poor network design. We approach this transition as a comprehensive architectural strategy.
Our advisory teams assess your entire digital footprint first, ensuring tool deployments directly support a unified security posture rather than creating new operational silos.
Ignoring Legacy Integration Complexity
Bridging decades-old on-premise hardware with modern cloud-native access controls creates severe technical friction. Forcing incompatible systems together often results in critical application downtime.
We engineer phased integration pathways utilising secure microservices. This practical approach of legacy system modernisation allows older applications to function safely within a modernised framework until they undergo complete digital product engineering or decommissioning.
Skills Shortages in Cybersecurity
Finding the specialised talent to design and manage complex network environments is one of the primary barriers to zero trust adoption in Australian enterprises. Projects stall simply because internal teams lack the required architectural expertise.
When you hire zero trust solution providers in Australia, our engineering pods work alongside your staff, bridging the knowledge gap while accelerating safe deployment.
Lack of Executive Alignment
Security upgrades that fail to secure ongoing board-level support frequently suffer from slashed budgets. If the initiative is framed purely as an IT expense, it will struggle to survive financial reviews.
We bridge this communication gap by tying architectural changes directly to quantifiable risk reduction metrics. This ensures consistent executive backing and clear commercial alignment throughout all execution phases.
Poor Identity Governance
Layering adaptive authentication over a messy, outdated active directory guarantees operational failure. If existing user roles are poorly defined, the new framework will simply enforce incorrect permissions faster.
We conduct rigorous identity hygiene assessments before deploying access controls. Cleaning up orphaned accounts and defining strict role-based parameters ensures your foundational directory is accurate, secure, and ready for migration.
Underestimating Cultural and Operational Change
Introducing new authentication workflows often triggers severe resistance from the workforce if poorly communicated. Employees will actively search for dangerous workarounds if security systems slow down their daily tasks.
We embed structured change management protocols into the deployment cycle. By utilising dynamic risk scoring, we minimize login friction for trusted behavior and ensure staff productivity remains completely unaffected.
The Core Technologies Powering Zero Trust Architecture
Executing a resilient zero trust architecture implementation in Australia requires integrating immediate technical controls with forward-looking telemetry. Executive boards must fund an interoperable stack that bridges legacy hardware with foundational identity controls today, while preparing for autonomous policy enforcement tomorrow to maintain strict governance over distributed assets.
Enterprise Technology Stack: Current vs. Future Outlook
| Operational Domain | Core Technologies (Current Focus) | Emerging Technologies (2026 Outlook) |
|---|---|---|
| Identity and Access | Identity Providers (IdPs), SSO, Privileged Access Management (PAM), Adaptive MFA | AI-powered behavioural authentication, passwordless authentication, machine identity management |
| Network Connectivity | Zero Trust Network Access (ZTNA), Secure Access Service Edge (SASE), Microsegmentation | Identity-native connectivity, autonomous policy enforcement, dynamic mesh networks |
| Endpoint and Threat Telemetry | Endpoint Detection and Response (EDR/XDR), Security Information and Event Management (SIEM) | Continuous risk scoring, predictive AI-driven threat analytics, automated self-healing response |
How Appinventiv Helps Aussie Enterprises Build Zero Trust Security Architectures?
Replacing an outdated network perimeter is a complex structural shift. If handled poorly, transitioning to an identity-first architecture introduces severe operational risk. Enterprise boards require execution certainty; they need absolute assurance that modernising access controls will neither halt daily productivity nor compromise existing compliance postures.
Ensuring this critical upgrade maintains commercial velocity while satisfying strict local governance standards requires an experienced digital product engineering partner in Australia like Appinventiv.
We bridge regulatory mandates with practical engineering to secure your infrastructure without disrupting daily enterprise operations. As an approved zero trust implementation partner in Australia and an active vendor on the Queensland Government ICTSS and Local Buy LGA procurement panels, we understand the exact legacy constraints your internal IT teams face.
This is why, when leadership teams look to hire zero trust solution providers in Australia, they rely on our proven execution capability to navigate this transition safely.
- Proven Enterprise Scale: We have successfully deployed over 3000+ digital assets across 35 industries, supported by five agile delivery centres nationwide and a 96 percent client retention rate.
- Rigorous Security Governance: Our internal operations maintain strict ISO 27001, ISO 9001, and SOC2 certifications, backing every enterprise deployment with a 99.5 percent security compliance SLA.
- Public Sector Readiness: We provide direct, fully compliant procurement pathways for government agencies through our active placement on the Queensland Government ICTSS and Local Buy LGA panels.
- Regulatory Alignment: Our certified architects map your existing legacy infrastructure directly against ACSC Essential Eight and SOCI Act mandates before altering any core access protocols.
We manage the deep technical integration, handle the workforce transition, and execute the architectural migration safely without halting your commercial momentum.
Ready to move from legacy security to a production-grade Zero Trust architecture? Schedule a Zero Trust readiness review with our enterprise engineering team today.
FAQs
Q. What are the core Zero Trust principles?
A. Zero Trust is built on three foundational principles: verify explicitly (authenticate and authorise every access request based on all available signals), use least privilege access (grant the minimum access required for the task, with time-bound and scope-limited permissions), and assume breach (design systems and controls as if a breach has already occurred, limiting blast radius through segmentation and continuous monitoring).
Q. What is Zero Trust Architecture and how does it work?
A. Zero Trust Architecture is a security model that removes implicit trust from enterprise networks. Every access request, regardless of origin (internal or external), is authenticated, authorised, and continuously evaluated before and during access. The architecture is implemented through a combination of identity controls, device trust, network segmentation, and continuous monitoring, rather than as a single product or solution.
Q. How do you implement zero trust architecture in Australia?
A. The steps of zero trust architecture implementation in Australia follow a phased approach: begin with a comprehensive discovery and assessment of identities, data flows, and existing controls; establish identity and device baselines, including MFA and IAM consolidation; implement microsegmentation and ZTNA for network-level controls; and then move to continuous monitoring, automation, and AI-driven analytics. Each phase should be aligned with the specific regulatory obligations relevant to the organisation, including the Essential Eight, SOCI Act, and Privacy Act requirements.
Q. Why should businesses adopt Zero Trust security in Australia?
A. The advantages of zero trust security model for Australian enterprises are both security-specific and compliance-driven.On the security side, Zero Trust reduces breach probability, limits lateral movement, and improves threat detection and response times. On the compliance side, Zero Trust controls directly support Essential Eight maturity requirements, SOCI Act risk management obligations, CPS 234 security capability requirements, and the data governance obligations of the Privacy Act.
Q. What should I look for in a zero trust implementation partner in Australia?
A. When evaluating a zero trust implementation partner Australia, the key criteria are demonstrated delivery experience across relevant sectors, depth in the specific regulatory frameworks that apply to your organisation (Essential Eight, SOCI Act, CPS 234, Privacy Act), certified practitioners in identity, cloud security, and network architecture, and the capacity to support both the technical implementation and the change management dimensions of the programme. Procurement panel approvals are relevant for government agencies. Client retention rates and reference availability are reliable indicators of sustained delivery quality over time.
Q. How long does zero trust implementation take?
A. A full Zero Trust implementation for a mid-sized Australian enterprise typically takes 12 to 18 months across four phases. The discovery and assessment phase runs for 6 to 8 weeks. Identity and device baseline implementation runs for approximately three months. Microsegmentation and ZTNA deployment runs for five to six months. The continuous monitoring and automation phase is ongoing but reaches operational maturity at around the 12-month mark. Larger enterprises with complex legacy environments should plan for 18 to 24 months.
Q. Can Zero Trust work with legacy systems?
A. Yes, though the integration requires careful design. Legacy systems that cannot be updated to support modern authentication protocols can be accommodated through identity proxies, API gateways, and controlled access pathways that apply Zero Trust controls at the boundary of the legacy system. The discovery and assessment phase should specifically map legacy system dependencies so that the architecture design accounts for them explicitly rather than treating them as exceptions to be resolved later.
Q. What industries benefit most from Zero Trust in Australia?
A. All industries benefit from Zero Trust, but the sectors where the combination of threat exposure, regulatory obligation, and operational complexity creates the strongest case are healthcare, banking and financial services, government and defence, mining and energy, and retail and eCommerce. In each of these sectors, the distributed nature of operations, the sensitivity of the data held, and the regulatory accountability of senior leadership make Zero Trust both a security necessity and a compliance imperative.