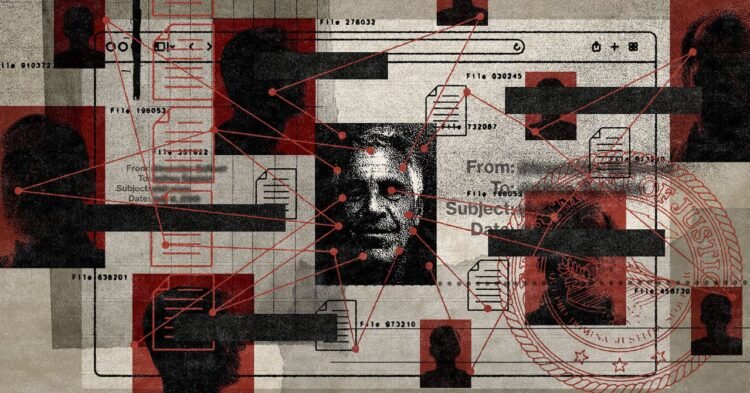
The Epstein Library on the Justice Department’s website is a model of disorganization. In early December, Keller was clicking through the tens of thousands of pages of documents in the library and feeling “frustrated disbelief” at the chaos—files that could be hundreds of pages long, text that was sometimes blurry or sideways, a wire transfer with no context, an email chain with half the names blacked out, a flight log with only initials. “It’s disorienting,” he says. “You’re reading fragments of something enormous and trying to figure out which fragments matter and how they connect.”
One night, he spent about four hours trying to trace a single person’s name across some 30 documents in the archive. “I just stopped and thought, I am doing by hand what a database could do in milliseconds,” he says. As a builder of database infrastructure at a midsize company, he knew exactly what to do next. “I opened a code editor and started building. By 3 am I had a basic search prototype working against a few hundred documents,” he says.
Around that time, a site called Jmail.world was making a splash as a tool for people to peruse Epstein’s emails as if using a Gmail interface. Launched in mid-November and built by a group of tech-savvy volunteers, it has since grown to include, among other things, his photos, flights, and Amazon purchase history, also displayed as if the reader is viewing Epstein’s own accounts. Keller used the tool and liked it. “Jmail was proof that the community could build better tools than the government was providing,” he told me.
It also helped him hone his own project. “Instead of thinking about one category of documents, I started thinking about the network,” he says. “How do you connect a person who appears in an email to a flight they were on, to a wire transfer, to a deposition they gave? That cross-referencing problem is what I wanted to solve.”
Then, on December 19, the Justice Department released its first big tranche, adding hundreds of thousands of new documents to the existing archive. Immediately, Keller’s workload ballooned to an all-time high. The prototype he had built earlier in the month became the foundation for processing all of it.
Most nights he worked until 3 or 4 am, sipping cold coffee while navigating a sea of open tabs.
Because of his childhood, he says, “when the first documents started dropping, I couldn’t look away. I understood at a gut level what was being described in those files.” In the evenings, he’d return home from his day job and, once everyone in his family was in bed, he’d hole up in his home office and spend hours scrolling through downloaded PDFs.
Many documents were posted as images, and he’d run each page through layers of software to convert them into searchable text—sometimes one system would fail to convert the text and he’d run it through a second or third. Then he’d use another system to extract important details such as names, organizations, dates, and locations. He’d perform hash verification—a process that checks whether the Justice Department’s files have been tampered with—and redaction analysis, to scan for inconsistencies in how the government blacked out information. He tracked all his work in a meticulous, digital, color-coded ledger. “It’s not uploading files,” he says. “It’s rebuilding a crime scene from 2 million fragments of evidence.”