Originally from the small Balkan country of Montenegro, Strahinja (Strajo) Janjusevic says his life has unfolded in unexpected ways, for which he is deeply grateful. After graduating from high school, he was selected to represent his country in the United States, studying cyber operations and computer science at the U.S. Naval Academy in Annapolis, Maryland. He has since continued his cybersecurity studies and is currently a second-year master’s student in the Technology and Policy Program (TPP), hosted by the MIT Institute for Data, Systems, and Society (IDSS). His research with the MIT Laboratory for Information and Decision Systems (LIDS) and the MIT Maritime Consortium team aims to improve the cybersecurity of critical maritime infrastructure using artificial intelligence, considering both the technology and policy frameworks of solutions.
“My current research focuses on applying AI techniques to cybersecurity problems and examining the policy implications of these advancements, especially in the context of maritime cybersecurity,” says Janjusevic. “Representing my country at the highest levels of education and industry has given me a unique perspective on cybersecurity challenges.”
Janjusevic’s pathway from Montenegro to Maryland was created by a program that allows selected students from allied countries to attend the U.S. Naval Academy. Janjusevic graduated with a dual bachelor’s degree in cyber operations and computer science. His undergraduate experience provided opportunities to collaborate with the U.S. military and the National Security Agency, exposing him to high-level cybersecurity operations and fueling his interest in tackling complex cybersecurity challenges. During his undergraduate studies, he also interned with Microsoft, developing tools for cloud incident response, and with NASA, visualizing solar data for research applications.
Following his graduation, he realized that he still needed more knowledge, particularly in the area of AI and cybersecurity. TPP appealed to him immediately because of its dual emphasis on rigorous engineering innovation and the policy analysis needed to deploy it effectively. Janjusevic’s experiences at TPP have been a big change from his time at the U.S. Naval Academy, with a different pace and environment. He has especially appreciated being able to broaden his understanding about a variety of research domains and apply the discipline and knowledge he earned during his time at the academy.
“My TPP experience has been amazing,” says Janjusevic. “The cohort is really small, so it feels like a family, and everyone is working on diverse, high-impact problems.”
Mitigating the risks of emerging technologies
Janjusevic’s thesis brings together disciplines of cybersecurity, AI and deep learning, and control theory and physics, focusing on securing maritime cyber-physical systems — in particular, large legacy ships. The hacking of these ships’ networks can result in substantial damage to national security, as well as serious economic effects.
“Strajo is working to outsmart maritime GPS spoofing,” says Saurabh Amin, the Edmund K. Turner Professor in Civil Engineering. “Such attacks have already lured vessels off course in contested waters. His approach layers physics-based trajectory models with deep learning, catching threats that no single method can detect alone. His expertise has been very helpful in advancing our work on threat modeling and attack detection.”
The research utilizes advanced threat modeling and vessel dynamics to train AI systems to distinguish between legitimate maneuvers and spoofed signals. It involves building a framework that employs an internal LSTM (long short-term memory) autoencoder to analyze signal integrity, while simultaneously using a physics-based forecaster to predict the vessel’s movement based on environmental factors like wind and the sea state. By comparing these predictions against reported GPS positions, the system can effectively distinguish between natural sensor noise and malicious spoofing attacks. This hybrid framework is designed to empower, not replace, human operators, providing verified navigation data that allows watch standers to distinguish technical glitches from strategic cyberattacks.
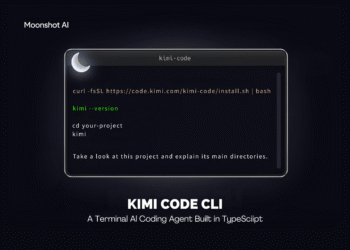
Sanjusevic has been able to enhance his academic research with industry experience. In summer 2025, he interned with the Network Detection team at the AI cybersecurity company Vectra AI. There, he investigated potential threats new technologies can bring, particularly AI agents and the model context protocol (MCP) — the emerging standard for AI agent communication. His research demonstrated how this technology could be repurposed for autonomous hacking operations and advanced command and control. This work on the security risks of agentic AI was recently presented in the preprint, “Hiding in the AI Traffic: Abusing MCP for LLM-Powered Agentic Red Teaming.”
“I was able to gain practical insights and hands-on experience into how a data science team uses AI models to detect anomalies in a network,” says Janjusevic. “This work within industry directly informed the anomaly detection models in my research.”
International policy perspective
“Strajo brings not just a high level of intelligence and energy to his work on cyber-physical security for merchant vessels, but also a strong instinct from his Navy training that resonates deeply with the research effort and grounds it in actionable policy,” says Fotini Christia, the Ford International Professor of the Social Sciences, director of IDSS and the MIT Sociotechnical Systems Research Center, and a leader of the MIT Maritime Consortium.
Janjusevic participates in the cybersecurity efforts of the Maritime Consortium, a collaboration between academia, industry, and regulatory agencies focused on developing technological solutions, industry standards, and policies. The consortium includes cooperation with some international members, including from Singapore and South Korea.
“In AI cybersecurity, the policy element is really important, as the field is so fast-moving and the consequences of hacking can be so dangerous,” says Janjusevic. “I think there’s still a lot of need for policy work in this space.”
Janjusevic is also currently helping to organize two upcoming major conferences: the Harvard European Conference in February, which will convene officials and diplomats from across the globe, and the Technology and National Security Conference in April, a collaboration of Harvard and MIT that brings together top leaders from government, industry, and academia to tackle critical challenges in national security.
“I’m striving to find a position where I can influence and advance the cybersecurity field with AI, while at the same time leading collaboration and innovation between the United States and Montenegro,” says Janjusevic. “My goal is to be a bridge between Europe and the U.S. in this space of national security, AI, and cybersecurity, bringing my knowledge to both sides.”