Key takeaways:
- Medical device software integration is a governance decision first. Define data ownership, clinical workflows, and regulatory scope before writing a single API.
- Build on recognized standards from the outset. FHIR, DICOM, and IEEE 11073 reduce ambiguity and simplify long-term scaling.
- Expect validation and security to drive real cost. Documentation, testing, and firmware controls often take more effort than core development.
- Design for uptime in real clinical environments. High availability, encrypted telemetry, and device authentication are mandatory in ICU and imaging settings.
- Work with teams that understand regulated healthcare delivery. An early, structured technical assessment can clarify scope, risks, and budget exposure before commitments are made.
For hospital networks, MedTech manufacturers, and large diagnostic groups, connected medical devices are no longer pilot initiatives. They sit at the core of clinical operations, revenue reporting, and regulatory accountability. Yet in many board-level reviews, one concern surfaces repeatedly: devices generate data, but the systems around them do not always speak the same language.
Research on clinical information systems shows that manual transcription of device-generated patient data can introduce delays and documentation errors, particularly when devices cannot send information directly to electronic medical records.
That reality changes the conversation. Integration is no longer a technical connector between a monitor and an EHR; it becomes an infrastructure decision affecting uptime, audit trails, cybersecurity posture, and long-term platform strategy.
Medical device software integration, when approached strategically, aligns firmware, middleware, interoperability standards, and compliance documentation into a governed framework. When approached tactically, it creates brittle interfaces and exposes the organization to regulatory risk.
This guide examines the difference and outlines how leadership teams can structure integration initiatives with the right architecture, validation model, and technical oversight from the outset.
Readmissions Lower Up to 25% When Remote Monitoring Data Flows Directly into Clinical Systems
Let’s evaluate if your medical device integration supports that level of reliability.
What Leaders Must Evaluate Before Initiating Medical Device Software Integration
In most hospitals, discussions about medical device integration begin after a trigger event. Sometimes it is a failed audit, and other times it is the clinician’s frustration with duplicate charting. Occasionally, a cybersecurity review exposes how loosely connected certain devices actually are. By that stage, urgency is high, and clarity is limited.
Medical device integration software should not begin with vendor selection. It should begin with structured internal alignment. Before comparing platforms or providers, leadership teams need to agree on scope, risk appetite, and operational objectives. That early discipline prevents expensive redesign later.
Below are the areas that deserve direct executive attention.
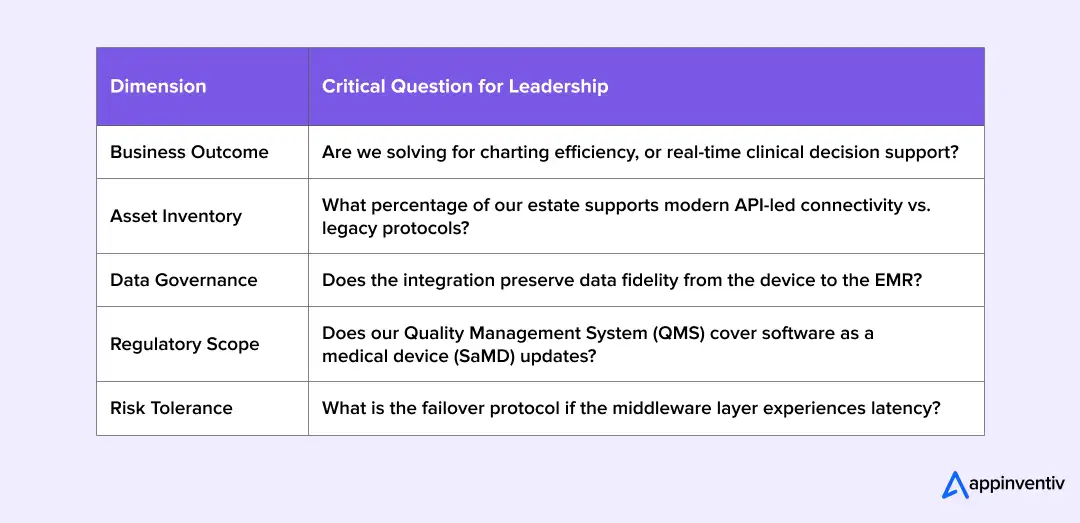
Define the Business Outcome, Not Just the Interface
Every medical device integration project must answer a simple question: what problem are we solving?
Reducing manual charting with EHR systems is different from building a real-time ICU command center. Similarly, medical device EMR platform integration to improve documentation accuracy has a narrower impact than enterprise-wide medical device data integration that feeds analytics or predictive models.
When the outcome is vague, integration becomes a technical exercise. When the outcome is measurable: reduced documentation time, improved device uptime, fewer reconciliation errors, architecture decisions become easier to justify at the board level.
Audit the Existing Device and System Estate
Many healthcare environments operate devices purchased over a ten-year window. Firmware versions vary, vendor support cycles differ. Some devices support modern medical device API integration, others do not.
A credible integration system plan requires a grounded inventory:
- Device types and models
- Firmware and patch status
- Supported protocols (HL7, FHIR, DICOM, proprietary formats)
- Current data flow paths
- Dependency on legacy middleware
This mapping exercise often exposes hidden constraints. In several large-scale projects, integration timelines shifted not because of coding complexity, but because a subset of devices required hardware upgrades before safe interoperability was possible.
A short discovery phase, sometimes facilitated through integration consulting, can clarify these constraints before contracts are finalized.
Examine Interoperability and Data Governance
Medical device data integration affects more than clinical dashboards. It influences billing accuracy, reporting integrity, and regulatory documentation.
Leadership teams should review:
- Whether FHIR or HL7 is used as a canonical data model
- How imaging data is handled under DICOM workflows
- How integration with EHR or EMR healthcare platforms preserves structured data fidelity
- Where data transformation occurs—at the device, middleware, or application layer
Without governance, medical device interoperability tends to accumulate one-off mappings. Over time, these create inconsistencies that are difficult to trace during audits.
Data lineage should be visible, and transformation logic should be documented. If that visibility is missing, it is worth pausing before expanding the scope.
Clarify Regulatory and Quality Management Responsibilities
Regulations and compliance to know during medical device system integration differ by jurisdiction and device classification. However, the underlying principle remains consistent: traceability matters.
Frameworks commonly affecting integration initiatives include:
- IEC 62304 for software lifecycle controls
- ISO 13485 quality systems
- FDA 21 CFR requirements
- Compliance with HIPAA and data protection laws
These are not abstract references. They influence logging strategy, validation documentation, change management controls, and incident reporting workflows.
Medical device software that does not align with documented validation processes increases audit exposure. Teams that integrate compliance checkpoints into their rollout plan typically experience fewer late-stage delays.
Assess Operational and Security Risk Early
Risk evaluation should extend beyond firewall configuration.
Consider:
- Device authentication mechanisms
- Secure firmware update procedures
- Middleware resilience under peak load
- Failover behavior in ICU or imaging environments
- Exposure created by expanding IoMT endpoints
Challenges in medical device data integration often surface during stress conditions rather than routine operation. Simulation testing and controlled load exercises can expose weak points before patient-facing deployment.
A structured review across these five dimensions forms the core components of a medical device integration strategy. It also provides clarity during cost analysis, since remediation and validation requirements become visible upfront.
Well-scoped programs rarely move the fastest at the beginning. They do, however, move more predictably, and that predictability is often what operational leadership values most.
Architecture Patterns for Medical Device Integration Systems
Architecture decisions have long-term consequences. They determine how easily new devices are onboarded, how data flows across systems, and how resilient the environment remains under load. In most hospital settings, the integration model available today could be five to ten years old.
The right model depends on device diversity, regulatory constraints, and expected scale. That said, most integration projects fall into one of four architectural patterns.
Middleware-Based Integration (The Enterprise Standard)
Middleware introduces an abstraction layer between devices and downstream applications. Instead of building direct links to each EHR or analytics system, devices connect to a centralized medical device software platform.
This layer performs protocol normalization, data transformation, and routing. It can translate proprietary device outputs into standardized formats, such as FHIR or HL7, simplifying medical device data integration across the organization.
Middleware-based medical device solutions offer several advantages:
- Reduced duplication of connectors
- Centralized monitoring and logging
- Simplified onboarding of new device types
- Improved visibility into data lineage
Vendor independence also improves. When downstream systems change, adjustments are made within the middleware rather than across dozens of device-level interfaces.
In practice, many healthcare organizations engage in medical device integration consulting during this stage to evaluate whether existing middleware can be extended or if a new integration layer is required.
Pros: Vendor independence; centralized logging.
Best for: Large hospital networks with multi-vendor device estates.
API-Led Connectivity (The Modern Modular Approach)
API-led architecture builds structured service layers on top of device data. In this model, medical device API integration exposes standardized endpoints that applications can consume securely.
This approach aligns well with modern EHR integration strategies. FHIR-based APIs allow structured exchange of observations, device metadata, and patient-linked measurements.
API-led models also support modular development. Clinical dashboards, analytics platforms, and patient-facing applications can evolve independently while consuming a consistent set of data services.
However, API-led architecture still depends on reliable device abstraction beneath it. Without a stable normalization layer, APIs simply expose inconsistent data faster.
For this reason, API-led connectivity is often implemented alongside middleware rather than replacing it entirely.
Pros: High flexibility; supports “Plug-and-Play” for new digital health apps.
Best for: Innovation-focused diagnostic groups and remote monitoring platforms.
Cloud-Native IoMT Platforms
As device volumes increase, especially in remote patient monitoring and multi-site deployments, cloud-native architectures become more relevant.
These platforms typically include:
- Telemetry ingestion pipelines
- Event-driven processing
- Scalable storage layers
- Real-time monitoring dashboards
- Edge-to-cloud orchestration
In cloud-based solutions, scalability improves significantly. New device cohorts can be onboarded without redesigning the core architecture.
Security and compliance controls, however, must be embedded carefully. Device authentication, encrypted communication, and controlled data-residency policies are essential components of any cloud-enabled system-integration strategy.
Pros: Infinite scalability for remote patient monitoring (RPM).
Best for: Multi-site deployments and post-acute care providers.
Point-to-Point Integration (The Legacy Trap)
Point-to-point integration connects each device directly to a target system, typically through custom interfaces.
At first glance, this model appears efficient. It supports rapid deployment for a limited number of devices and works well in low-complexity single-site environments.
The challenge emerges over time. As device counts grow, so does the number of custom connectors. Each new integration increases maintenance overhead, and changes to one system often require adjustments across multiple interfaces. In environments with medical device integration with EMR or EHR platforms, even minor schema updates can cascade into repeated rework.
This approach is rarely suitable for large-scale integration system initiatives. It may serve as a temporary solution, but it does not scale predictably.
The Risk: Creates a “spaghetti” of interfaces that are nearly impossible to maintain or audit.
Choosing the Right Architectural Pattern
For large hospital networks or MedTech manufacturers, a hybrid model often proves to be the most resilient. Middleware handles device abstraction and protocol normalization. API layers provide structured access to downstream systems. Cloud components enable scalability and cross-site coordination.
Architecture selection should not be based solely on vendor marketing materials. It requires technical validation against the organization’s device inventory, regulatory obligations, and expected growth trajectory.
In many cases, a structured architectural review or proof-of-concept phase clarifies whether the proposed software integration stack can sustain projected scale. Investing in that assessment early reduces risk later, particularly when analysing the cost of integrating medical devices, including long-term maintenance and compliance considerations.
Well-designed architecture does not simply connect systems. It creates a governed foundation that can evolve without repeated disruption.
Interoperability Standards That Matter in 2026
Architecture determines how systems connect. Medical device interoperability standards determine whether those connections remain reliable over time.
In medical devices, the question is rarely whether we support HL7 or FHIR, but how consistently those standards are implemented and governed across devices, middleware, and downstream systems.
Below are the standards that materially influence the software integration initiative in 2026.
HL7 and FHIR: Beyond Transport
HL7 v2 continues to operate in many medical devices with EMR environments. It supports structured message exchange, particularly in legacy systems.
FHIR, however, now anchors most modern integration with EHR strategies. Its resource-based structure allows device observations, metadata, and patient context to be represented consistently.
The governance issue is version control and profile consistency. If FHIR resources are implemented differently across departments or vendors, the integration becomes inconsistent. Over time, that inconsistency surfaces during audits or analytics initiatives.
DICOM in Imaging-Heavy Environments
Where imaging is central: radiology, cardiology, oncology; DICOM compliance becomes critical.
Medical device system integration involving imaging equipment must account for metadata conventions, storage standards, and transmission performance. Small variations in tagging can affect reporting and retrieval from archives.
Unlike numeric telemetry feeds, imaging integration often stresses infrastructure. Performance testing under a realistic load is advisable before scaling the deployment.
Also Read: How Much Does DICOM Medical Imaging Software Development Cost?
Device-Level Communication Standards
IEEE 11073 remains relevant in environments that require a consistent representation of physiological measurements.
While not universally adopted, alignment with device communication standards reduces the need for custom mapping logic in medical device software platforms.
Where proprietary protocols are unavoidable, documentation discipline is essential. Integration decisions made here directly affect long-term maintenance costs.
Security as an Interoperability Requirement
In 2026, interoperability cannot be separated from security.
Medical device APIs must include authentication controls, encrypted transmission, and mechanisms for traceable updates. Regulatory scrutiny increasingly extends to supply-chain transparency and software component documentation.
Security failures often present first as integration failures.
The Governance Question
The most important question is not which standards are supported. It is how those standards are governed.
- Are FHIR profiles standardized internally?
- Is DICOM metadata interpretation documented?
- Are interface changes version-controlled?
- Are interoperability test results archived?
Organizations that formalize this layer experience fewer disruptions during system upgrades or audits. Standards, when treated as policy rather than technical footnotes, stabilize medical device integration over time. Without that discipline, even well-designed architectures begin to fragment.
Also Read: How AI is Revolutionizing Data Governance for Enterprises?
Compliance, Risk Management, and Validation in Medical Device Integration
Compliance is not a downstream activity for medical device software. It shapes architecture, documentation, and deployment timelines from the outset. When medical device software integration proceeds without structured validation planning, audit findings typically surface later, often at the worst possible moment.
Below are the elements that require deliberate attention.
Regulatory Alignment
Regulations and compliance to know during system integration depend on geography and device classification, but several frameworks frequently apply:
- IEC 62304: Software lifecycle processes.
- ISO 13485: Quality management for medical devices.
- DICOM/HL7/FHIR: The “languages” of interoperability.
- SOC2/HIPAA: The baseline for data privacy.
FDA QMSR Update (Effective Feb 2, 2026)
The FDA has revised 21 CFR Part 820 into the Quality Management System Regulation (QMSR), formally incorporating ISO 13485:2016 by reference. This alignment changes terminology and inspection focus and raises the bar on traceability, supplier controls, risk justification, and documentation structure.
For integration projects, this means stricter expectations for RTMs, supplier-facing evidence (for third-party middleware or device vendors), risk-based design decisions, and audit-ready deliverables (for example, Medical Device Files and Design & Development Files instead of legacy QSR labels).
Plan a short QMSR scoping step early in your integration roadmap to confirm documentation formats and inspection readiness.
These standards influence how integration solutions handle change management, traceability, logging, and incident reporting. If regulatory responsibilities are unclear between internal teams and the service provider, gaps appear quickly.
A brief compliance scoping exercise before development begins often prevents redesign later.
Validation and Verification Planning
Medical device data integration must be verifiable, not assumed. Validation typically includes:
- Requirements traceability matrices
- Interface validation testing
- Regression testing after system updates
- Controlled environment simulations
When integrating mobile devices with EHR or EMR systems, even small data mapping errors can affect billing or clinical documentation. Structured validation reduces that risk.
Where device ecosystems are complex, an independent technical review or consulting engagement can help confirm that validation coverage is sufficient.
The 21 CFR Principle
If it isn’t documented, it didn’t happen. Integration initiatives must include a Requirements Traceability Matrix (RTM) that links every clinical requirement to a specific test case and result.
Risk Management and Cybersecurity Controls
Risk management for enterprises should extend beyond application-layer testing.
Key areas include:
- Device authentication mechanisms
- Secure firmware update processes
- Encrypted telemetry channels
- Failover procedures during outages
Challenges in medical device data integration often surface during peak usage or system upgrades. Testing under realistic load conditions is advisable before full-scale rollout.
Security weaknesses often first appear as integration failures.
Documentation and Audit Readiness
The integration cost of a medical device often overlooks documentation effort during analysis. Yet audit artifacts, test reports, and change logs require disciplined maintenance.
At a minimum, projects should maintain:
- Documented interface specifications
- Version-controlled configuration records
- Logged system events with retention policies
- Clear ownership of compliance artifacts
Well-documented system integration initiatives move more predictably through regulatory reviews.
Compliance and validation may not be the most visible components of medical device software integration, but they are often the most consequential. Teams that treat this layer seriously from the beginning reduce disruption later, both operationally and financially.
Planning Device Integration in a Regulated Environment?
Validate your architecture, documentation scope, and risk exposure before scaling across facilities.
Medical Device Integration Use Cases Across Healthcare Segments
When leadership teams evaluate, they usually ask one practical question: Where has this worked in the real world? Below are documented medical device software integration examples that illustrate how structured device integration changes care delivery and operations.
Device-to-EHR Integration at Scale — MU Health Care (United States)
MU Health Care undertook a large-scale device connectivity program that linked bedside monitors, ventilators, and other clinical equipment directly to its EHR. Instead of relying on manual transcription, device-generated vitals flowed automatically into structured patient records.
The study notes measurable improvements in documentation timeliness and a reduction in manual entry errors after devices were connected across multiple units. That shift required interface engines, standardized message formatting, and disciplined testing before rollout.
For hospital CIOs, this example underscores a central point: integration of medical devices with EMR systems is not a cosmetic upgrade. It affects clinical workflow, billing accuracy, and audit readiness.
AI-Enabled e-ICU Monitoring — Noida District Hospital (India)
In 2026, MMG District Hospital in Noida introduced an AI-enabled e-ICU command centre. Bedside monitors in the ICU feed patient vitals into a centralized dashboard where remote specialists can review data in real time.
The significance here is structural. Continuous medical device data integration enables tertiary care teams to monitor multiple units without being physically present. It is not simply video conferencing; it is device-level telemetry routed securely and consistently.
For health systems managing specialist shortages, this model shows how integration can expand clinical reach without expanding physical footprint.
Patient-Generated Data Integrated into EMR Systems
A peer-reviewed systematic review published via PubMed Central examined large-scale integration of mobile health applications into EMR/EHR systems. Across more than 100,000 patients, structured transmission of home-monitored metrics, such as glucose readings and blood pressure, improved clinician access to longitudinal data.
The research highlights an operational insight: integration of medical device software is no longer limited to bedside hardware. It now includes mobile-connected sensors and home-use devices that feed structured observations into clinical records.
For digital health leaders, this expands the scope of medical device data integration. Governance, interoperability standards, and validation processes must extend beyond hospital walls.
Wearable Device Ecosystems and Interoperability Research
A recent academic review of digital health research examined how wearable technologies connect to provider systems via standardized APIs and interoperability layers. The authors emphasize that without structured API-based integration, wearable telemetry remains isolated from clinical workflows.
This reinforces a strategic lesson. Integration of medical device API is not about connecting “another app.” It requires data model normalization, secure transmission, and alignment with EHR schemas.
For organizations expanding into remote monitoring or chronic disease projects, architectural discipline at this stage determines long-term scalability.
Also Read: Trends Underpinning Wearable App Development in 2026
Device Log Analytics to Improve Clinical Workflows
A research study indexed in PubMed Central analyzed aggregated device logs across hospital systems to understand workflow inefficiencies. By studying how devices were used and when, researchers identified bottlenecks and process gaps that were not visible through traditional reporting tools.
This types of medical device Integration analysis are only possible when the software captures normalized device telemetry and consistently stores it. Without that foundation, operational analytics remains fragmented.
For operations leaders, this example illustrates how integration supports not only clinical visibility but also performance improvement and resource planning.
A Common Thread Across These Projects
Across geographies and care models, these cases share several characteristics:
- Structured, standards-based integration rather than ad hoc connectors
- Early validation to prevent downstream mapping errors
- Clear governance around device onboarding and data ownership
- Measurable operational impact, not just technical connectivity
For teams considering the integration of medical devices, these examples suggest a practical approach: start with a scoped assessment, validate interoperability assumptions, and define clinical objectives before scaling across facilities.
Integration, when approached methodically, becomes a long-term infrastructure investment rather than a short-term IT project.
Also Read: Medical Device Software Development Guide
What Factors Influence the Cost of Medical Device Software Integration?
Budget conversations tend to begin with software pricing. In reality, licensing is only one component. The more significant cost drivers sit in architecture alignment, validation effort, and long-term operational sustainability.
For leadership teams, it helps to separate visible development expenses from structural investments that influence the total cost of ownership.
Cost Drivers: Analyzing Total Cost of Ownership (TCO)
Licensing is often the smallest line item. Enterprises must budget for the integration’s “Full Lifecycle”.
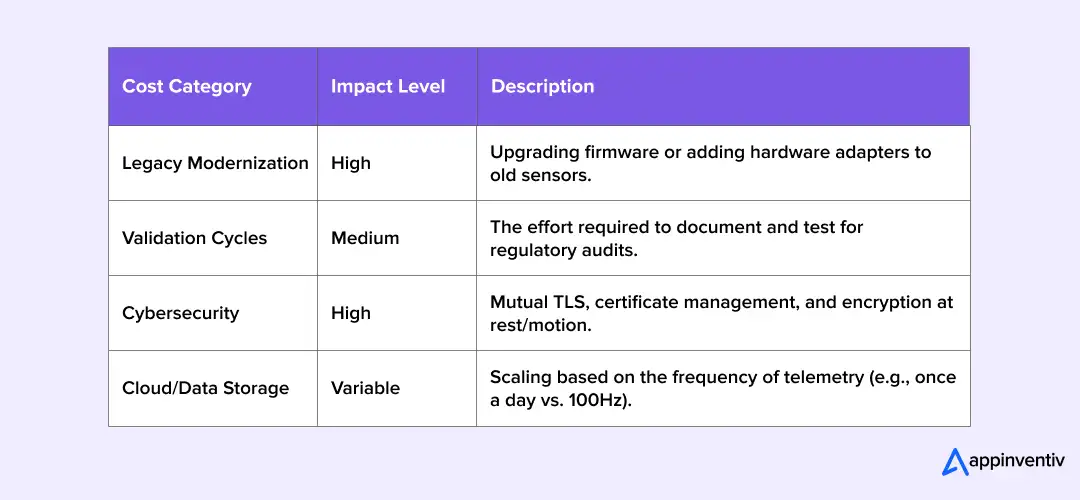
1. Legacy Device Modernization
Older devices often lack modern interface capabilities. Some require firmware updates, while others depend on proprietary communication protocols that demand custom adapters.
In multi-site hospital environments, even small variations to modernize legacy systems in healthcare device models can introduce additional integration layers. The cost here is not only engineering time; it is testing, documentation, and maintenance across versions.
2. Middleware and Integration Layer Development
A structured medical device integration software layer, whether custom-built or commercially licensed, forms the backbone of the system.
Costs typically include:
- Interface engine configuration
- Protocol normalization logic
- Development of API integration
- Monitoring and logging frameworks
Organizations that skip architectural validation often underestimate the effort required to support future device onboarding. A short technical assessment before build-out can provide more accurate projections.
3. Regulatory Documentation and Validation Cycles
Compliance rarely appears as a line item in early project proposals, yet it materially influences cost.
Validation testing, traceability matrices, audit artifact preparation, and regression cycles add measurable effort. For medical device integration with EMR or EHR systems, structured data mapping verification is mandatory.
Businesses operating under IEC 62304 or ISO 13485 controls must rigorously document change management and testing. That discipline affects timelines and budget allocation.
4. Cybersecurity Hardening
Medical device system integration expands the attack surface. Security architecture must account for:
- Device authentication
- Encrypted data transmission
- Secure firmware updates
- Network segmentation
- Logging and anomaly detection
Cybersecurity implementation is not an optional enhancement. It is part of responsible planning for the integration of medical device data. Underestimating this component often leads to mid-project cost adjustments.
Also Read: Key Strategies for Ensuring Cybersecurity in Healthcare
5. Cloud Infrastructure and Scalability
For distributed health systems or remote monitoring initiatives, cloud infrastructure becomes a significant cost factor.
Expenses include:
- Data storage and retention
- Real-time telemetry processing
- Redundancy and high-availability design
- Ongoing monitoring and support
A hybrid model that combines on-premises middleware with cloud-based analytics is common. The long-term cost profile depends heavily on data volume growth.
Cost Model Overview
Medical device integration typically follow one of three commercial approaches:
Custom Integration (Higher CAPEX)
- Greater upfront investment in architecture and development.
- Better control and long-term scalability.
SaaS-Based Middleware (Operational OPEX)
- Lower initial implementation cost.
- Recurring subscription and potential vendor dependency.
Hybrid Approach
- Balance between control and operational flexibility.
- Often selected for phased multi-facility rollouts.
Indicative ranges observed in hospital deployments:
| Limited-scope integration (single department or pilot) | $40,000 to $120,000 |
|---|---|
| Mid-scale hospital integration | $250,000 to $1.5 million |
| Multi-site system-wide rollout | $2 million and above |
Actual figures vary based on device diversity, regulatory requirements, cybersecurity controls, interoperability complexity, and validation depth.
Looking at Cost Through an ROI Lens
While integration projects require structured investment, their financial impact is not limited to expense.
Common measurable returns include:
- Reduced manual documentation effort
- Fewer reconciliation errors
- Lower risk of compliance penalties
- Improved visibility into device utilization
- Extended lifecycle management of connected equipment
For procurement and technology leaders, the more relevant question is not simply “What will this cost?” but “What operational exposure remains if we do not integrate properly?”
A scoped discovery workshop or architectural review can clarify these variables before formal budgeting begins. In regulated healthcare environments, that early clarity often proves more valuable than aggressive cost reduction.
Common Integration Failures and the Technical Fixes That Prevent Them
Medical device integration projects rarely fail because the idea was flawed. They fail because critical engineering controls were either underestimated or postponed.
Below are recurring failure points seen in medical device software integration initiatives, along with the corrective measures typically implemented by experienced integration partners.
1. Firmware and Device Variability Not Accounted For
In multi-vendor environments, devices often run different firmware versions, even within the same unit. Small variations in payload structure or timestamp formatting can disrupt the integration of medical device data.
Mitigation:
A disciplined integration vendor begins with a device profiling phase. This includes:
- Creating a device inventory mapped to firmware versions
- Building test harnesses that simulate device outputs
- Validating compatibility before live deployment
- Maintaining a structured device registry for future upgrades
This approach reduces unexpected interface breaks during updates.
Expert Tip: Always request a documented firmware compatibility matrix before expanding device onboarding.
2. Inconsistent Data Mapping Across Systems
Many medical device EHR integration initiatives assume that data mapping is straightforward. In practice, unit conversions, observation codes, and contextual metadata differ across vendors.
Mitigation:
A structured canonical data model, often FHIR-based, is defined before full-scale development. Integration specialists then implement:
- A transformation layer with version-controlled mapping rules
- Automated schema validation
- Regression testing for mapping changes
- Clear documentation of data lineage
Vendors with deep experience in API integration typically maintain reusable mapping frameworks to reduce duplication across projects.
3. Performance Bottlenecks Under Clinical Load
Medical device system integration may function correctly in controlled testing but fail during peak clinical hours. Telemetry bursts from ICUs or remote monitoring projects can overload message queues or database layers.
Mitigation:
Experienced integration teams conduct:
- Telemetry replay simulations using real-world traffic patterns
- Load and stress testing across edge and cloud components
- Failover scenario validation
- Capacity planning with defined throughput thresholds
Without these measures, scalability assumptions remain theoretical.
Expert Note: Performance testing should reflect real patient volumes, not lab simulations with minimal device streams.
4. Offline Data Integrity in Disconnected Device Scenarios
Clinical networks are not always stable. Devices may temporarily lose connectivity due to network transitions, gateway failures, or routine maintenance.
Without safeguards, this can result in missing readings, duplicate records, or gaps in the clinical timeline. In environments where device telemetry feeds EHR documentation or monitoring dashboards, even brief outages can cause downstream reconciliation issues.
Mitigation:
Resilient medical device integration architectures typically include:
- Local edge buffering on device gateways
- Store-and-forward data transmission
- Message queue persistence for temporary outages
- Timestamp validation during replay synchronization
- Duplicate detection during reconnection
These controls ensure that patient telemetry collected during offline periods is safely transmitted once connectivity is restored.
Expert Tip: Always test reconnection scenarios during integration validation. Many failures only appear when devices reconnect after a network interruption.
5. Cybersecurity Controls Implemented Too Late
Security gaps frequently emerge when device connectivity expands rapidly. Weak authentication or unencrypted telemetry introduces exposure in IoMT-heavy environments for healthcare.
Mitigation:
A structured medical device integration solution incorporates:
- Mutual TLS authentication between devices and gateways
- Certificate-based device identity management
- Encrypted data transport
- Secure firmware update workflows
- Network segmentation aligned with zero-trust principles
Integration vendors familiar with regulated healthcare environments embed these controls into the architecture rather than layering them afterward.
6. Compliance Documentation Not Embedded in the Process
Initiatives sometimes treat regulatory documentation as a closing activity. In regulated healthcare, that sequencing leads to rework.
Regulations and compliances to know during system integration, such as IEC 62304 and ISO 13485, require traceability from requirements through validation.
Mitigation:
A structured approach includes:
- Requirements-to-test traceability matrices
- Automated evidence capture during validation
- Version-controlled interface specifications
- Audit-ready change management logs
Integration providers with healthcare domain experience typically align development workflows with quality management frameworks from the beginning, reducing downstream audit risk.
7. No Clear Ownership of Integration Governance
Over time, software environments evolve. Without defined ownership, the mapping logic and interface rules fragment.
Mitigation:
Mature integration teams recommend:
- Governance committees overseeing device onboarding
- Version-controlled API documentation
- Periodic interoperability reviews
- Formal change control processes
In large-scale programs, organizations often engage external technical advisors to review governance maturity before expansion into additional facilities.
8. Time Synchronization Drift Across Devices
Medical devices and hospital systems do not always operate on perfectly synchronized clocks. In multi-device environments, even small differences in timestamps can create problems when data from monitors, infusion pumps, or wearable sensors is aggregated in clinical systems.
If time drift occurs, patient events may appear out of sequence in the EHR, which can affect clinical review, audit trails, and the accuracy of analytics.
Mitigation:
- Integration architectures typically address this by:
- Synchronizing systems using NTP or centralized time servers
- Applying timestamp normalization in the middleware layer
- Validating event order during data ingestion
- Monitoring clock drift across device fleets
Ensuring consistent time synchronization helps maintain reliable patient timelines and accurate system logs.
Lessons from the Field: Preventing Common Failures
Based on our experience at Appinventiv, these three “Technical Fixes” prevent 90% of mid-project collapses:
- Firmware Fingerprinting: Create a registry of every firmware version in your facility. A minor update on a ventilator shouldn’t break your EHR bridge.
- Load Replay Testing: Don’t just test one device. Simulate 500 devices sending data simultaneously to see if your middleware chokes.
- The “Shadow IT” Audit: Ensure clinicians aren’t bypassing the integration layer with unauthorized apps that create data silos and security holes.
Future Trends in Medical Device Integration Platform in 2026
The trends in medical device software integration are shifting from connectivity alone to measurable operational impact. In boardrooms, the discussion is no longer about “can we connect this device?” It is about whether the integration layer supports financial sustainability, compliance resilience, and clinical performance targets.
Below are developments that are already influencing budget allocation and technology roadmaps.
1. Predictive Analytics Built on Device Telemetry
Hospitals now sit on years of structured device data: ventilator readings, infusion patterns, cardiac telemetry, and more. When this information is normalized through medical device data integration pipelines, it becomes usable for predictive modeling.
Early deterioration alerts, staffing forecasts, and ICU utilization analysis are becoming common use cases.
The financial return is not abstract. Reduced adverse events, shorter ICU stays, and improved bed turnover translate into measurable cost containment. However, predictive systems only function when a medical device ensures time-synchronized, high-fidelity data streams.
Organizations exploring this direction often begin with a targeted data quality audit before expanding into analytics initiatives.
Also Read: 10 Uses Cases of Predictive Analytics in Healthcare
2. Edge-Enabled Processing in High-Acuity Settings
Cloud adoption continues to grow, yet certain environments cannot tolerate latency. Intensive care units, operating rooms, and emergency departments increasingly adopt edge-enabled integration of medical devices.
Edge processing enables local analysis of device telemetry before forwarding it to centralized dashboards. If network connectivity drops, monitoring continues uninterrupted.
Operational outcomes include:
- Reduced downtime risk
- Improved system resilience
- Lower bandwidth strain in multi-site networks
From a cost perspective, preventing even short monitoring interruptions in high-acuity areas can avoid significant clinical and reputational risk.
When planning modernization, many technology teams conduct architectural workshops to determine where edge processing adds value versus where centralized systems suffice.
3. Remote Monitoring as a Revenue and Capacity Strategy
Remote patient monitoring initiatives continue expanding beyond pilot phases. Wearables and home-use diagnostic devices now feed structured observations into EHR systems through API integration frameworks.
The operational impact is visible:
- Earlier discharge planning
- Reduced readmissions
- Better chronic disease oversight
Financially, remote monitoring supports value-based reimbursement models and frees inpatient capacity for higher-acuity cases.
However, integrating consumer and clinical-grade devices into structured records requires careful validation. Without consistent mapping and alignment on compliance, scaling such projects becomes difficult.
Also Read: How Much Does it Cost to Develop a Remote Patient Monitoring Software?
4. Predictive Maintenance Through Device Utilization Data
Integrating medical device software increasingly captures not only clinical metrics but also device utilization logs and performance indicators.
Aggregated telemetry enables predictive maintenance scheduling. Rather than servicing equipment on fixed intervals, organizations can intervene based on actual usage patterns.
The outcome is twofold:
- Reduced unplanned device downtime
- Extended equipment lifespan
Capital planning benefits directly. Procurement cycles become data-informed rather than reactive.
5. Stronger Audit and Traceability Controls
Regulatory scrutiny is intensifying across jurisdictions. As integration complexity grows, so does the need for structured audit trails.
Emerging approaches include immutable logging frameworks and enhanced device identity controls tied to SBOM documentation. While not every organization adopts advanced distributed ledgers, the emphasis on traceable change management is increasing.
The ROI here lies in risk mitigation. Avoiding compliance penalties, audit findings, and reputational damage often outweighs the cost of implementing structured traceability mechanisms.
What These Trends Signal for Leadership Teams
Each of these developments shares a dependency: reliable integration solutions at the foundation.
Advanced analytics, remote monitoring expansion, predictive maintenance, and stronger compliance controls all depend on:
- Standardized interoperability
- Secure device authentication
- Version-controlled APIs
- Ongoing validation discipline
Organizations planning for 2026 and beyond often conduct structured readiness assessments before investing in advanced capabilities. Evaluating whether the current integration layer can sustain these initiatives prevents fragmented upgrades in the future.
In short, trends are accelerating, but only those with a stable integration backbone can convert them into measurable outcomes.
Vendor Evaluation Checklist for Enterprise Buyers
Vendor selection rarely fails because of missing on the key features of medical device integration. It fails when assumptions remain untested. A strong proposal should withstand technical scrutiny, regulatory review, and operational stress testing.
Below is a practical evaluation framework used by hospital CIOs and digital health leaders during vendor shortlisting.
1. Can the Vendor Demonstrate Real-World Integration Depth?
Ask to see architecture from completed medical device projects, not marketing diagrams.
Look for:
- Experience in medical device integration with EMR or EHR platforms
- HL7, FHIR, and DICOM implementation details
- Handling of proprietary device protocols
- Evidence of medical device API integration in production environments
A credible partner should walk through normalization logic, not just say “FHIR-compliant.” The conversation should include mapping governance, version control, and upgrade strategy.
If the vendor avoids technical walkthroughs, that is a signal in itself.
2. Is Regulatory Discipline Embedded in Delivery?
Medical device integration software in healthcare environments intersects with regulated processes.
You should be able to ask:
- How is IEC 62304 alignment handled?
- Where is the traceability matrix maintained?
- How are validation logs archived?
- What documentation is handed over at go-live?
Vendors experienced in regulated system integration typically show redacted validation packs or testing artifacts. If compliance appears as an afterthought, risk increases later.
3. Does the Security Architecture Extend to the Device Layer?
Medical device data integration expands the attack surface.
Clarify whether the services provider supports:
- Device-level authentication (certificate-based identity)
- Encrypted telemetry transport
- Secure firmware update workflows
- SBOM documentation practices
- Independent penetration testing
Security discussions should not remain abstract. They should reference specific technical controls.
4. How Mature Is the Delivery Process?
Integration is not a one-time deployment.
Evaluate:
- CI/CD pipelines with automated interface testing
- Regression testing after device onboarding
- Performance testing methodology under peak loads
- Incident response and SLA commitments
Vendors with structured solutions often propose phased rollouts. That reduces disruption during scale-up.
5. Is Cost Transparency Aligned With Long-Term Sustainability?
The medical device integration cost analysis should extend beyond the initial implementation.
Ask:
- What are ongoing support costs?
- How are change requests handled?
- What happens when device models change?
- Is there clarity around scaling to additional facilities?
Unexpected cost escalations typically emerge from unclear scope boundaries rather than technical complexity.
A Practical Shortlisting Approach
Before finalizing contracts, some healthcare organizations conduct a technical validation workshop. During this session, vendors review:
- A subset of real device payloads
- Sample EHR integration points
- Compliance documentation templates
- Performance expectations
This approach often surfaces capability gaps early.
Vendor evaluation in medical device integration is less about comparing slide decks and more about assessing engineering discipline. The right partner should demonstrate structured processes, documented validation, and operational readiness.
Ready to Convert Device Data into Reliable Clinical Workflows?
Schedule a short technical review to map the device estate, compliance scope, and phased rollout.
How Can Appinventiv Help with Regulated Medical Device Integration?
Appinventiv offers medical device software development services as a disciplined engineering programme, not a one-off IT project.
Our services start with a short, focused discovery to map devices, firmware, protocols, and the scope of compliance. That inventory drives a phased plan: pilot → core services → scale.
Core Capabilities We Bring
These capabilities reflect the engineering controls, governance discipline, and validation rigor required for long-term success in integrating medical software development services into regulated healthcare environments.
- Cross-functional teams: firmware, cloud, integration, clinical informatics and compliance engineers working under a single technical lead.
- Device profiling & test harnesses: registry of models/firmware/protocols with SBOM links and device emulators for safe onboarding.
- Canonical data model & mapping registry: FHIR-based resources, versioned mapping rules, automated schema checks and unit tests.
- Middleware + API pattern: normalize device outputs in middleware; expose consistent FHIR/REST APIs or HL7 bridges.
- Validation & audit artifacts: RTM, regression suites, signed test reports and an audit-ready validation pack.
- Security by design: device identity (certs/TPM), mutual TLS, SBOM tracking, signed OTA and routine pentests.
- Performance & resilience testing: telemetry replay, soak/burst tests and a capacity plan.
- Post-go-live support & governance: runbooks, change control, SRE/DevSecOps monitoring and API lifecycle management.
If you want to validate your current approach, consider a scoped technical assessment: 2–4 weeks of device discovery, conformance checks (FHIR/DICOM), and a short report with remediation priorities and a phased roadmap. That assessment converts unknowns into a costed plan ready for procurement.
If you’d like to run this assessment, connect with our healthcare engineering team to schedule a technical discussion.
Frequently Asked Questions
Q. What is Medical Device Integration?
A. In simple terms, medical device integration means allowing clinical devices to “talk” directly to hospital software systems.
Every hospital uses dozens—sometimes hundreds—of devices that record patient information: bedside monitors, infusion pumps, ventilators, imaging equipment, and more. Traditionally, much of that data had to be typed into the patient record by staff.
With proper integration in place, the device sends the information straight into systems like the EHR or monitoring dashboards. The reading captured by the device is the same one that appears in the patient chart.
For clinical teams, that removes an extra step. For the organization, it creates a more reliable stream of patient data across systems.
Q. What are the benefits of medical device integration?
A. Most hospitals notice the benefits first in everyday workflows.
When device readings flow automatically into clinical systems, nurses and technicians spend far less time copying numbers from screens into charts. That small change can save a surprising amount of time across an entire shift.
Accuracy improves too. Because the data moves directly from the device, there’s less chance of transcription mistakes.
There are longer-term advantages as well. Integrated device data makes it easier to monitor trends, review how equipment is being used, and analyze care patterns across departments. Over time, those insights help improve both patient care and operational planning.
Q. What should we look for in a medical device integration SLA?
A. An SLA for medical device integration should answer one basic question: what happens when something goes wrong?
Hospitals usually focus on a few practical areas. Uptime guarantees are important, especially when device data supports critical care units. Response times for technical incidents should also be clear—who gets notified and how quickly the issue will be addressed.
It’s also worth looking at how updates are handled. Devices receive firmware changes, and hospital systems evolve over time. The SLA should explain how those updates will be tested and rolled out without interrupting clinical workflows.
Security expectations—things like encryption, logging, and audit support—are another key part of the agreement.
Q. How much does enterprise medical device integration typically cost?
A. The cost of an enterprise medical device integration is not fixed, and anyone who gives one upfront is usually oversimplifying.
If you’re connecting a limited set of devices within a single department, budgets often start at around $40,000 and can rise to $100,000 depending on validation and security scope. A hospital-wide medical device software integration initiative—covering multiple device classes and full medical device integration with EHR—commonly ranges from $250,000 to $1.5 million. Multi-facility rollouts, especially those involving remote monitoring or advanced analytics, can exceed $2 million.
The real variables are device diversity, firmware inconsistency, compliance documentation effort, cybersecurity controls, and long-term support planning. Many health systems choose to run a short discovery or technical assessment first, simply to avoid budgeting blind.
Q. What technologies are used to integrate medical devices?
A. Most medical device initiatives rely on a mix of medical device interoperability standards and middleware infrastructure.
You will typically see:
- HL7 v2 or FHIR for integration with EHR platforms
- DICOM in imaging-heavy environments
- IEEE 11073 for device communication structures
- Interface engines or middleware layers for normalization
- REST-based APIs for controlled data access
- Secure transport protocols and certificate-based authentication
The stack is rarely greenfield. It usually needs to coexist with legacy systems already in place. That’s why architectural fit often matters more than selecting the “latest” toolset.
Q. What systems can medical devices connect to (e.g., EHR, PACS, LIS)?
A. With structured integration system, devices can exchange data with:
- EHR or EMR systems for automated charting
- PACS platforms for imaging storage and retrieval
- LIS environments for laboratory workflows
- Pharmacy and infusion management systems
- Clinical decision support tools
- Remote patient monitoring dashboards
- Data warehouses used for operational analytics
The complexity is not in the connection itself. It’s in keeping the data model consistent, time-synchronized, and audit-ready across all systems.
Q. How does integration improve patient care and clinical workflow?
A. The first impact is usually operational. Nurses and clinicians spend less time transcribing readings from bedside monitors into records. That reduces charting delays and documentation errors.
The second impact is clinical visibility. When device-generated vitals flow directly into the care record, alerts can trigger earlier. Trends become easier to interpret. Remote monitoring programs gain structured, reliable data rather than isolated dashboards.
Over time, integration also supports equipment utilization tracking and workflow analysis. Hospitals often find that once device telemetry is normalized, it becomes a source of operational insight—not just documentation.
In most cases, the improvement is incremental rather than dramatic on day one. But as more devices come online under a governed integration framework, those incremental gains compound.
Q. How long does a typical enterprise medical device integration project take?
A. A small pilot project—say, integrating monitors in one department—might take three or four months once testing and validation are included. Larger programs that connect devices across multiple units or facilities typically take closer to six to twelve months.
A lot depends on the starting point. Hospitals with a large mix of device models or legacy systems often need more time for compatibility testing.
Many organizations begin with a short discovery phase to catalogue devices and integration points. That step doesn’t take long, but it usually makes the rest of the project move much more smoothly.